ince its introduction in 2009, Bitcoin has often been described as the “money of the future.” Unlike traditional currencies, Bitcoin is not issued by governments or managed by banks, but instead runs on a decentralized computer network. This makes it unique: money that anyone in the world can use without relying on a bank in between.
Bitcoin is more than just a new form of digital money – it represents a completely new financial system, one that could fundamentally transform the role of banks.
🔗 How the System Works
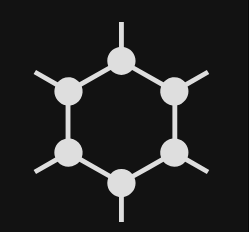
At the core of Bitcoin lies the blockchain: a public, immutable ledger that records every transaction. Unlike banks, which maintain their own closed databases, this ledger is open to all. Thousands of computers worldwide – called “nodes” – validate and confirm each transaction using cryptography.
✔ Every transaction is transparent and verifiable
✔ Manipulation is virtually impossible
✔ No one can block transfers or freeze accounts
In short: everyone becomes their own bank. 🏦
🚀 Where Bitcoin Shows Advantages
1. Faster and Cheaper Payments
International bank transfers often take several days and come with high fees. With Bitcoin, money can be sent worldwide within minutes – regardless of borders, bank holidays, or business hours.
Example: In 🇸🇻 El Salvador, Bitcoin became the world’s first official legal tender in 2021. Citizens saved millions in remittance fees. However, since January 29, 2025, the mandatory acceptance rule has been repealed: Bitcoin may still be used voluntarily, but it is no longer legal tender.
2. Inflation Protection Through Scarcity
Bitcoin’s supply is limited to 21 million coins. This scarcity protects against inflation, as no authority can “print” more of it.
Example: In countries suffering from high inflation 📉 such as Venezuela or Turkey, people increasingly use Bitcoin as a store of value to protect their savings.
3. Financial Inclusion
More than 1.4 billion people worldwide remain unbanked. With Bitcoin, all they need is a smartphone 📱 and internet access to participate in the global financial system – to save, receive, and send money.
Example: In Nigeria and Kenya, Bitcoin adoption is booming as young entrepreneurs use it to receive international payments when traditional banks are costly or restrictive.
4. Independence and Freedom
Banks can reject transactions or freeze accounts. In the Bitcoin network, this is impossible. Anyone can send or receive money at any time, without needing approval.
5. Integration Into the Global Economy
Bitcoin is no longer a niche phenomenon – major companies are adopting it:
- 🚗 Tesla invested about $1.5 billion in Bitcoin in 2021. In 2022, the company sold roughly 75% of its holdings, but as of Q2 2025 still holds about 11,509 BTC, worth around $1.2–1.24 billion.
- 💳 PayPal allows millions of users to buy, hold, and spend Bitcoin
- 🏦 Even major banks such as JPMorgan now offer Bitcoin-related services
🌍 A Glimpse Into the Future
If Bitcoin adoption continues, the financial world could look very different:
- 💸 Payments would be instant, global, and peer-to-peer
- 🔐 Savings would be kept in secure digital wallets instead of bank accounts
- 📊 Loans and investments could run through decentralized finance platforms (DeFi), eliminating banks as middlemen
- 🌐 Equal access for all: anyone, anywhere, can take part in the financial system
In this scenario, banks would no longer serve as gatekeepers. Instead, they might evolve into service providers, offering security, advice, or integration between traditional and digital finance.
✨ Conclusion
Bitcoin is far more than a digital currency. It is a tool for financial self-determination and a step toward a more open, decentralized economy. Examples from El Salvador, inflation-stricken nations, and large companies like Tesla and PayPal show that Bitcoin is already reshaping the financial world.
The future may hold a financial system that belongs to everyone – while banks adapt to entirely new roles. 🌍